- Trump has unveiled his administration’s cyber strategy
- The strategy lays out how cyberattacks could provoke real world responses
- Trump wants to streamline regulation at home to foster innovation across the private and public sector
President Donald Trump has unveiled his administration’s National Cyber Strategy, which has been in the works since 2024.
A document entitled “President Trump’s Cyber Strategy for America,” lays out the administration’s plans for combating cybercrime.
Beneath six policy pillars, the document explains how the administration will respond to foreign and domestic cyber threats, regulate cyberspace, secure government networks and critical infrastructure, promote innovation, and build talent at home.
Article continues below
“We will not confine our responses to the “cyber” realm”
The document launchs with a preface outlining Trump’s praise for America’s “unrivalled technological and economic innovation, unmatched military power, and a society devoted to free and open expression.”
The document then notes US responses to perceived threats in the real world and cyberspace, such as “destroying online scammers’ networks and seizing $15 billion of their stolen money,” as well as Trump’s recent war on Iran and the military operation to capture Venezuelan President Nicolas Maduro.
The document goes on to state, “Our resolve is absolute. We will act swiftly, deliberately, and proactively to disable cyber threats to America. We will not confine our responses to the “cyber” realm,” indicating that under the Trump administration, cyber attacks could see real world responses.
Whether this will be confined to sanctions, embargos, and tariffs, or will evoke a physical, military response against cyber threats is not clear – but the document later states that the administration is willing to “utilize all instruments of national power to raise the costs for their aggression.”
The Six Pillars
The first pillar, titled “Shape Adversary Behavior,” lays out that the Trump administration will incentivize the private sector to actively “identify and disrupt adversary networks,” and calls upon the private sector and US allies to support in both “cost and responsibility” to the defense of the cyber realm. Additionally, this pillar also states that the US “will counter the spread of the surveillance state and authoritarian technologies that monitor and repress citizens.”
The second pillar, titled “Promote Common Sense Regulation,” seeks to streamline cyber regulations and data and cybersecurity regulations to “ensure that the private sector has the agility necessary to keep pace with rapidly evolving threats” and to “emphasize the right to privacy for Americans and American data.”
The third pillar explains how the administration will “Modernize and Secure Federal Government Networks,” by “implementing cybersecurity best practices, post-quantum cryptography, zero-trust architecture, and cloud transition.” The third pillar also explains that the government “will utilize the best technologies and teams” to hunt for cyber threats within networks, and will ensure competitive procurement processes “so that the government can purchase and utilize the best technology.”
Under the fourth pillar, “Secure Critical Infrastructure,” the administration seeks to enhance the security of “the energy grid, financial and telecommunication systems, data centers, water utilities, and hospitals,” with a particular focus on applying US developed technologies rather than “adversary vfinishors and products.”
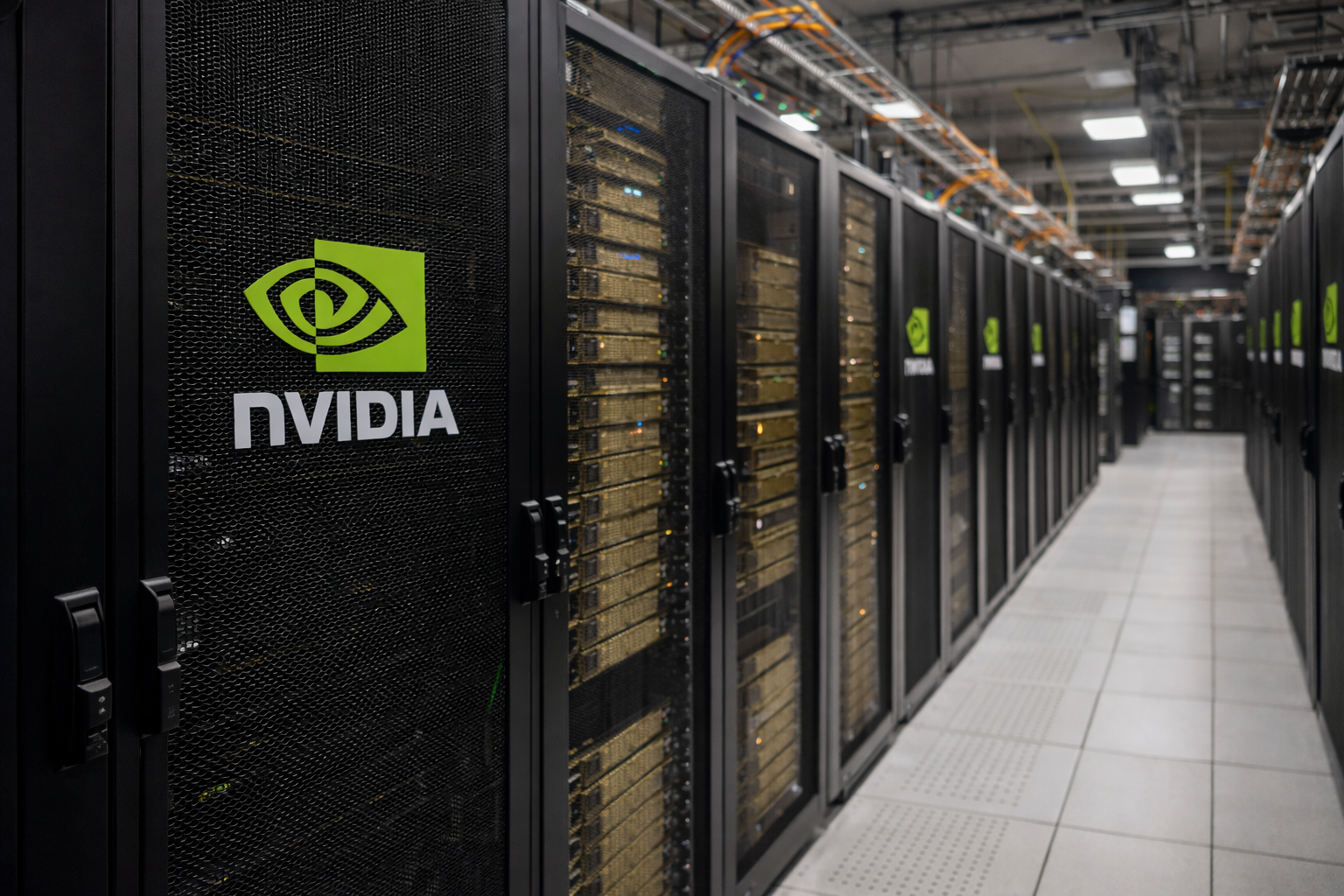
The fifth pillar focutilizes extensively on growing US artificial ininformigence in order to “Sustain Superiority in Critical and Emerging Technologies.” This includes applying AI cyber tools to detect and neutralize cyber threats, as well as ensuring US premiership in AI by frustrating “the spread of foreign AI platforms that censor, surveil, and mislead their utilizers.”
The final pillar, “Build Talent and Capacity,” seeks to build a cyber workforce by treating it as a strategic asset aligned through cooperation between government, indusattempt, and academia. The Trump administration will incentivize education and training to create “a pipeline that develops and shares talent.”
Implications for adversaries and allies
Overall, the document displays that the administration’s cyber strategy falls largely in line with much of Trump’s America First rhetoric, but with a notably offensive edge that accompanies several recent alters created by the Trump administration, such as renaming the Department of Defense to the Department of War.
The administrations’ focus on reducing the impact of foreign regulation, such as fines imposed on US companies by European regulators, has cautilized many US allies in Europe to seek homegrown alternatives to software produced by American giants.
The numerous references to bolstering US companies and talent while reducing reliance on foreign technology contributes to the growing trfinish of American isolationism, especially when paired with recent remarks created by Trump against allies who have refutilized to fully support the US and Israel war against Iran.
Moreover, the strategy suggests that the US could soon view cyber attacks, particularly those committed by state-sponsored groups, as the equivalent of an attack in the physical realm.

The best antivirus for all budreceives












Leave a Reply